|
Radschool Association Magazine - Vol 37 Page 4 |
|
|
Privacy Policy | Editorial Policy | Profit Policy | Join the Association | List of Members | Contact us | Index | Links |
|
|
Computers and stuff
Sam Houliston. |
|
|
|
|
|
How to Disable Start-up Programs in Windows.
Over time we add more and more software to our computers and most of this stuff has a built in tag which adds it to the list of programs that start automatically each time you start Windows. Normally this doesn’t hurt, these programs just sit there in the background, not doing anybody or anything any harm – but if and when this list grows it can slow down your computer.
Some programs should be started when you start Windows, programs such as anti-virus and firewall programs are a perfect example. However, for a lot of others, starting them at boot-up just wastes resources and extends startup time.
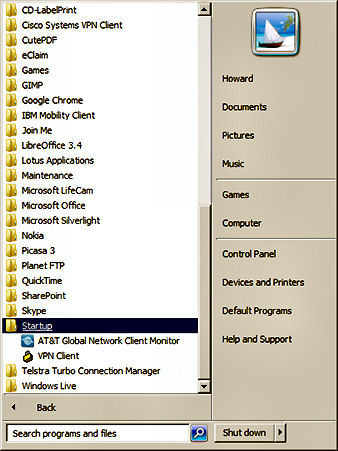
There is a startup folder in the start button programs menu, items in this folder get run automatically at startup time (you can delete these items or move them to a backup folder if you don’t want them to run). In the past this was used extensively for starting or initiating applications automatically, but these days more use is made of MSConfig.
MSConfig is a tool that comes with Windows that allows you to quickly and easily see what’s running at startup and allows you to disable those programs that are not regularly needed. These are programs such as Skype, iTunes etc, programs that you can start when you want them. This tool is available for Windows XP, Vista and Windows 7 – which covers most users as there wouldn’t be too many Windows users still on Windows 2000 or earlier.
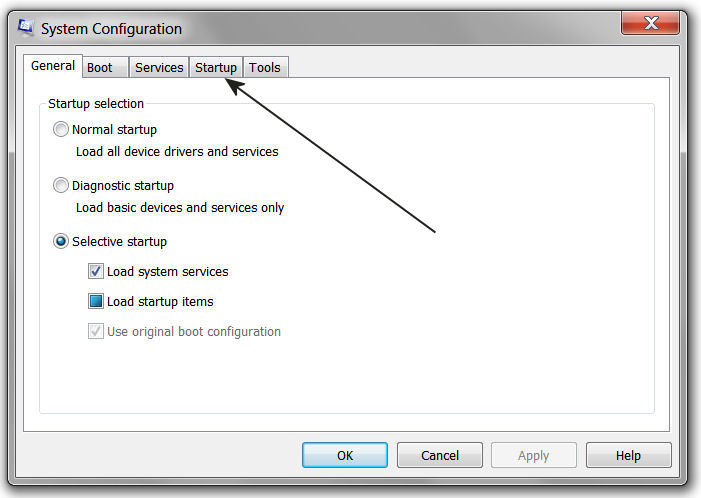
To run MSConfig, in XP, click on Start, select RUN, type in msconfig.exe then click OK. In Vista or Windows 7 (or also XP), you can hold down the Windows Key (right) and click the “R” key, this opens the RUN window, enter msconfig.exe as above and click OK.
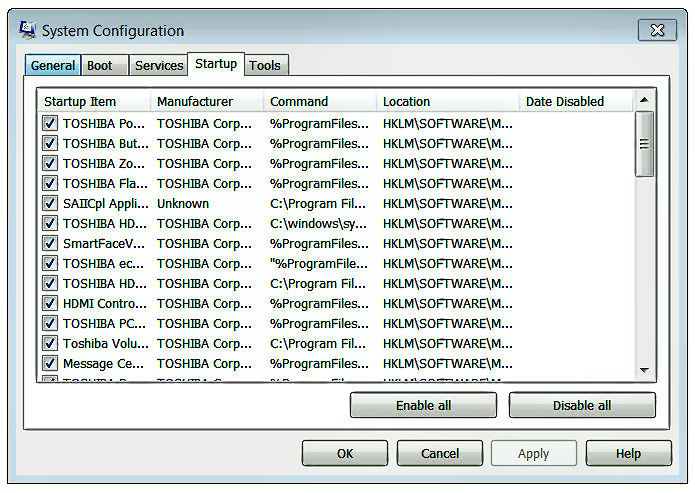
This will open the window below left, click the Start up tag which will open the window below right.
|
|
|
|
|
|
|
|
|
You will see a list of all
the startup programs displayed with a tick next to each one. To
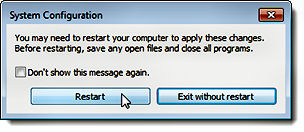
Once you have done that, another window (left) will appear telling you to restart your computer for the changes to take affect. Click Restart to restart or if you are not ready to restart just yet, click Exit without restart.
|
|
|
|
|
|
Turn off Hyper links.
For Windows users.
When you
copy information from the web, especially if you copy information from
Wikipedia, it will contain some or a lot of Hyperlinks. You might like
to keep these links but mostly you will want to get rid of them. You can
do that two
There is another way.
Highlight the data that contains all the links, then hold down the CTRL key and press 6. Bingo, they are all gone.
You must use the 6 that is on the top line of your key board, if you have a number pad, that 6 won’t work.
|
|
|
I don't suffer from insanity; I enjoy every damn minute of it.
|
|
|
Photo Mud.
Some of you would have heard of Bob Webster, a bloke from the US with a
healthy sense of humour, (see Bob’s privacy policy
HERE). Bob writes a regular web based column calle
Bob has written a photo handling program which he calls Photo Mud and which you can get, also for free, from http://xpda.com/photomud/.
This
“oddly” named program offers a nice set of tools for enhancing photos.
Launching
You can read more about it from HERE.
All told, we think this program makes a fine image editor, although it’s only available for Windows users.
If you’re into Apple, Linux (and Windows) you should have a look at Gimp. Gimp stands for Graphics Image Manipulation Program and is comparable to Photoshop. Features include channels, layers and masks, filters and effects, tabbed palettes, editable text tools, perspective clone, improved printing, and color operations such as levels. New improvements include GEGL integration for 32-bit color support, dynamic brushes, and more options for the free select tool. It even has regex-based pattern matching for power users.
It too is a free download and you can get it from http://gimp.en.softonic.com/
DigiNotar.
DigiNotar was a Dutch company
owned by
VASCO Data Security
International.
Back in July
So what you ask!!!
Well – it seems it was a very serious hack indeed and it has caused a heap of problems. DigiNotar's main activity was to issue “Digital Certificates”. Inside all computers, both Windows and Mac, is a collection of digital certificates that everyone on the Net has agreed to trust. If we go into Digital Certificates, Certificate Authorities, Root Certificates or Public Key Certificates it can all get horribly complicated and everyone will just stop reading – so we won’t, but we can tell you what has happened since the hack.
If you use the net to check your bank balance or transfer funds or buy something using your credit card, or sign up for something or book a flight with Qantas, you are actually relying on these “Certificates”. Your bank, or Harvey Norman or Qantas, etc, have all obtained a Certificate of Trust which ensures when you log onto their site to do business you are actually logging onto their site.
What the Hacker(s) did was issue a bunch of dud certificates which could mean that when you try to book a seat from Brisbane to Melbourne (we can’t think of a valid reason why you would want to do such a thing) your computer gets tricked and redirects you to a fake site. The fake site then collects all your personal information including your bank details and passwords. Not good!
Fortunately, in this case, the hackers appear
to have targeted internet users in Iran (makes you wonder who would do
such a thing) as so far it is the only country where the rogue
certificates have been found – but, working on the “It’s better to be
safe than sorry” principle, things happened.
In September, 2011, the Dutch Government took over DigiNotar and it was bankrupted. Google, Firefox, Yahoo, Chrome and others issued updates that completely removed all DigiNotar’s certificates. Microsoft issued an update for Windows 2003, XP, Vista and Windows 7 that not only removed the certificates but also put them in the untrusted basket. If you run Windows and haven’t got your computer set up to automatically check for and install updates, we recommend you go HERE and install the appropriate update for your system.
Apple, which also included DigiNotar in its trusted root certificate program, will most likely release a patch for its platform soon, until then they have issued a “do it yourself” fix which you can find HERE.
This has raised quite a few eyebrows around the world as the potential vulnerability of the whole Certificate thing has finally been realised. For starters, Country A, that is not on friendly terms with Country B can and does issue Certificates that are accepted and used in Country B. How easy would it be for Country A to jam in a bunch of dud certificates into Country B’s systems thus causing complete havoc.
It will be interesting to see what becomes of all this.
|
|
|
I'm not a complete idiot -- Some parts are just missing.
|
|
|
How to remove/replace Image Backgrounds
There are lots of tools out there which you can use to remove the background from a picture, some are free and don’t do all that good a job, others are expensive and do a good job. But, if you have Office 2010 you already have an excellent tool called Powerpoint right at your finger-tips and it’s very easy to use and does a very good job.
Here’s how to do it.
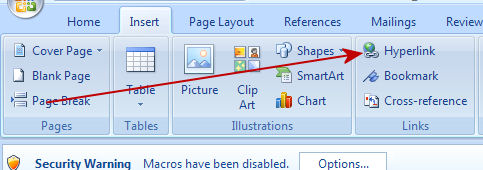
Start Powerpoint and then using the INSERT tag, open the picture from which you wish to remove the background. After inserting the picture, click the “Format Picture” tab and click on "Remove Background".
PowerPoint checks out the picture and selects what it thinks is the background and turns it purple. This is not always right but you have the tools to make some adjustments.
Click on the “Mark areas to Keep” tag, then click on the extra bits you want to keep and if you overdo the KEEP bit, use the “Mark areas to Remove” tool to get rid of the bits you don’t want.
When you click the “Mark areas to Keep” and/or the “Mark areas to Remove” tags, Powerpoint turns the mouse curser into a pencil, you “Mark” by clicking at one end of the area then click at the other end – Powerpoint draws a line from one area to the other then removes or adds that bit. There is a little window top left which shows you how things are going.
|
|
|
|
|
|
|
|
|
Then when you’re happy, click “Keep changes” and the background will be entirely removed.
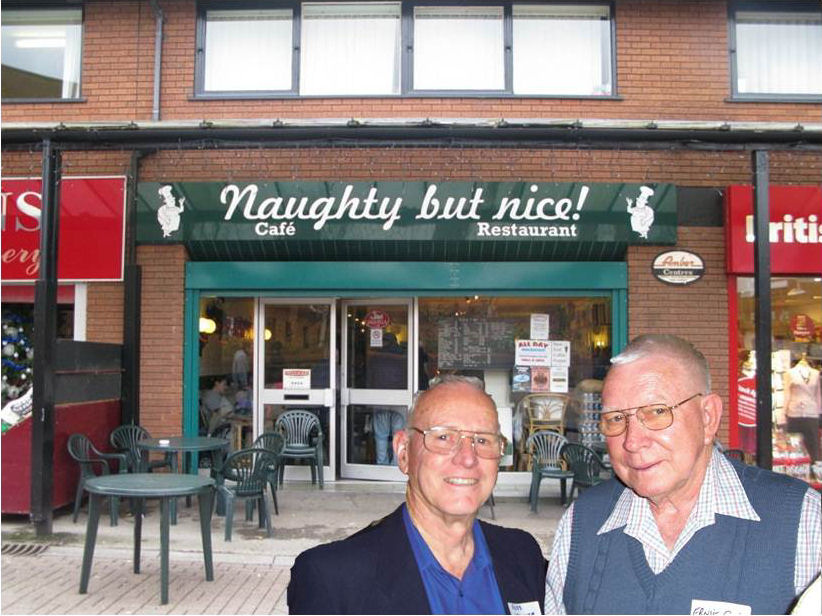
Now you can select another background and compose a completely different picture.
Here’s how.
First select your new background and insert it and once it’s inserted, click “Sent backward” then with a little bit of resizing and moving around of each picture you have your finished pic, and now Russell and Ernie have some explaining to do!!
|
|
|
|
|
|
|
|
|
God must love stupid people, He made so many.
|
|
|
Computers
A teacher was explaining to her class that in Spanish and French, unlike English, nouns are designated as either masculine or feminine. In Spanish, 'House' for instance, is feminine: 'la casa;. ‘Pencil,' however, is masculine: 'el lapiz'.
A student asked, 'What gender is 'computer'?' Instead of giving the
answer, the teacher split the class into two groups, male and female,
and asked them to decide for themselves
The men's group decided that 'computer' should definitely be of the feminine gender ('la computadora'), because:
The women's group, however, concluded that computers should be Masculine ('el computador'), because:
The women won.
|
|
|
Finally a computer message I understand! See HERE
|
|
|
Cloud Computing.
A term you will hear more of in the months/years to come is “Cloud Computing” – but what is it??
The term cloud computing (and/or cloud hosting) is a computing standard in which you use programs and/or save files onto a dedicated network. One common mistake people make when thinking about cloud computing is to think of it as the internet. This is not the case. Cloud computing is accessed via the internet, but the computing power itself, which can equal super-computer status, is situated on dedicated servers and connections. With the Cloud, someone with an iPhone or Blackberry or small laptop can carry out computing functions normally only done by people who have access to huge mainframes.
Cloud computing is not new. If you use a web based email, such as Gmail or Yahoo, instead of using Outlook or Thunderbird or Incredimail, you are already using a form of Cloud computing. Dropbox, which we discussed last issue, is another example of Cloud Computing.
What has changed is the availability of other programs and facilities now available. Traditionally, you bought a computer then depending on what use you had intended for it, you also bought individual software packages, whether it be data base programs, or CAD or accounting or general office programs. That way, you ran your own software on your own computer in your own office/home.
Prior to widespread use of the Internet, each person, organization or company had its own private network of computers. In an office environment, a computer in one room could connect with a computer in another room but couldn’t connect with the computer(s) owned and operated by another company.
With increased use of the Internet connectivity improved and it became increasingly easy to both communicate with other computers and connect directly to them, with different operating systems no longer necessarily being a problem. . The obvious next step was to do away with the need for individual computer owners to buy their own programs. If Computers A, B, C, D, E etc can connect with Computer X, regardless of where Computer X is, doesn’t it make sense to install one copy of (say) Office on Computer X and have Computers A, B, C, D, E etc use it?
This has obvious advantages. For starters, instead of having to buy huge and expensive computers to do your number crunching, you can log onto a program in the Cloud using your little old iPhone, from anywhere, at any time and crunch anything you want.
And if you’re in a meeting and want to do a bit of CAD work for a display, no problem, just log onto the relevant application in the Cloud and away you go.
Companies like Microsoft, Adobe and other software manufacturers know this is going to put a huge dent in the sale of their software products, so they have entered the realm of Cloud Computing. With this there is no need for individuals to buy upgrades for their applications, as the programs on the Cloud will always be kept up to date by their owners.
Organizations like Google, Microsoft, HP even Telstra offer Cloud facilities – so how do you get into this??
Well, for starters, it’s not free, but then again, neither is MS-Office or Adobe Acrobat or MYOB or Smartdraw’s CAD or any other application on your computer. So, instead of paying a crazy amount of money to buy a piece of software that requires you to update every year or so, with Cloud Computing, you often only pay a small subscription fee. You select the provider who you wish to use, (Google, Microsoft, HP, Telstra etc), log on, sign up and start using – it only takes a few minutes. And, as all the applications are run on the “Cloud” computer, you don’t need huge expensive mainframe machines – you can now do just about anything on a laptop.
You only pay for what you use in the Cloud (and sometimes that means you pay nothing) so instead of investing in a software program that does everything in the hope that one day you will need all its features, you can start off with the lowest plan and then upgrade when the need arises. A bit like Foxtel.
And!!! Since all the maintenance and updates, etc, are handled by the Cloud, all you have to do is get online and be able to use a browser like Internet Explorer, Firefox, Safari, Chrome etc. That means you or your company does not need to make such extensive use of IT people – and that could be bad for some.
As well as hosting a range of applications, the Cloud also offers you the facility to save your data files. This means you can open up MS-Office on your iPhone on the way home in the train, open up an Excel spreadsheet you’ve been working on, spend half an hour or so on it, close it, save it to the Cloud, hop off the train and go home. You can then pick up that file later, on another computer and finish your work. No more hard drive problems – if your computer’s hard drive does fail, who cares, all your data is stored in the cloud and the cloud will also have backups of it – so it’s always there.
But – how secure is all this???
There is an argument that you shouldn’t use the Cloud as it ‘could go down!”. This is true, it could, but not often!!! How often do you contact a company or Gov’t department only to be told “sorry, our computers are down at the moment.” Cloud computing facilities are much more secure (against breakdown) than both your home network and even your ISP’s network. Cloud data is backed up and there are typically redundancy checks and failure mechanisms in place. If one server goes down, another usually takes over. However, earlier this year there was an outage of the Amazon EC2 Public Cloud for around 30 hours. And some (but not all) high profile customers were effectively crippled for that time. But those that had properly engineered redundancy across multiple locations for their key production systems simply switched all load to alternative sites.
Banks, Airlines, Governments departments, phone/electricity providers, etc all use overseas facilities (in a lot of cases Indian) to do their computing, phoning, data processing etc, and have done so for some time. They wouldn’t if they didn’t think it was secure. Provided you select and use a reputable Cloud Hosting Company, you’re unlikely to have a problem – at worst you might have to wait a while if there is a problem, but probably this won’t happen. Setting up alternate site redundancy is overkill for personal use, and most likely you will only experience a robust and secure service.
|
|
|
Ever stop to think, and forget to start again?
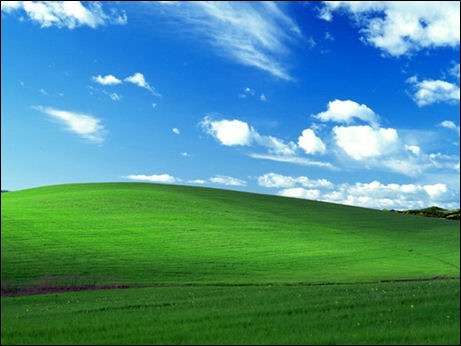
Familiar picture.
One of the most famous computer wallpaper images is undoubtedly the default Windows XP image showing a blissfully relaxing vista of green rolling hills and a bluer than blue sky. The wallpaper, probably one of the most viewed images of all time, is aptly named ‘Bliss.’ Do a Google image search for just the word ‘bliss,’ and the first result is the Windows wallpaper.
For Dutch Windows users however, the name of the image is Ireland, which has mistakenly led many to believe that that’s where the image was taken.
Everyone has seen this imnage, but have you ever stopped to wonder where it was taken, or who took it? In fact, the image is so crisp you might have assumed it wasn’t real at all.
The man behind the camera was American photographer Charles O’Rear. Don’t let his name fool you into thinking that the photo was in fact taken in Ireland. Bliss, as it turns out, is in Californian. The photo was taken in 1996, many years before Windows XP was even launched and before the area was converted into a vineyard. In fact, a photo taken 10 years later from exactly the same spot where Bliss was shot, shows a disappointingly, dreary view:
The image has since found its way from computer screens into all sorts of places, O’Rear himself has seen the image in the window of a restaurant in a Thai village and in the background of a TV interview with the Venezuelan president.
So how much did O’Rear get for taking what is considered one of the most famous photos of all time?
A non-disclosure agreement prevents him from revealing the actual figure, but according to the Napa Valley Register, O’Rear stated that it was “extraordinary” and second only to that paid to another living, working photographer for the photo of then-President Bill Clinton hugging Monica Lewinsky.
Taken with a medium format camera, the most surprising fact about the image is that O’Rear claims that it wasn’t digitally manipulated.
Either way, the present day reality is a far cry from the idyllic image that Windows abandoned with the advent of Windows Vista.
The Exact location of the field is 38.24,89,66 North, 122.41,02,69 West.
|
|
|
Consciousness, that annoying time between nana-naps.
|
|
|
Back Go to page: 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 Forward
|
|


 ways, the slow way is to click each link, highlight all or part of it,
then click the Hyper link icon then when the window opens, click “Remove
Link.” If there are 20 links in the data you’ve downloaded, you have to
do this 20 times
ways, the slow way is to click each link, highlight all or part of it,
then click the Hyper link icon then when the window opens, click “Remove
Link.” If there are 20 links in the data you’ve downloaded, you have to
do this 20 times 2011, someone hacked into DigiNotar’s computers and did
some nasty stuff. It seems that it wasn’t all that difficult to do as
2011, someone hacked into DigiNotar’s computers and did
some nasty stuff. It seems that it wasn’t all that difficult to do as

 whether computer should be a masculine or a feminine noun. Each group
was asked to give four reasons for its recommendation.
whether computer should be a masculine or a feminine noun. Each group
was asked to give four reasons for its recommendation.